CTO Community India: Software Vulnerability Assessment in the Era of AI
The CTO Community India recently hosted its fifth milestone series, pivoting from its previous explorations of AI , Quantum and Startups to the pressing frontier of Cyber Security in the AI Era.
Led by Anupama Itikirala, Founder of Mayuk Enterprises, and moderated by Richa Kumari , the session provided a masterclass in navigating the “new normal” where code is generated in seconds, but vulnerabilities can last a lifetime.
The Session Agenda:
- Career Resilience: Anupama’s 30-year journey from Enterprise Architect to a “Tech for Good” consultant.
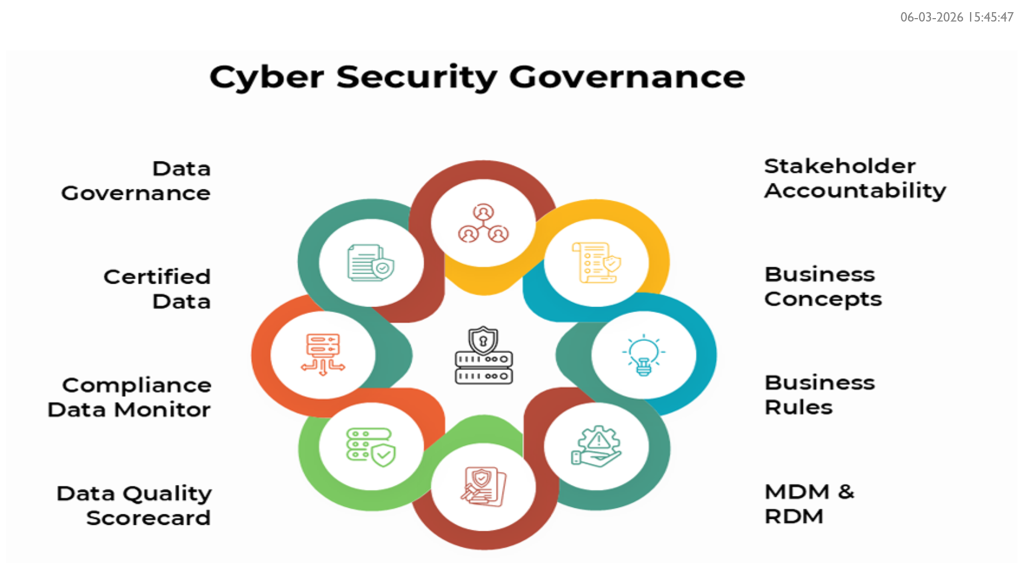
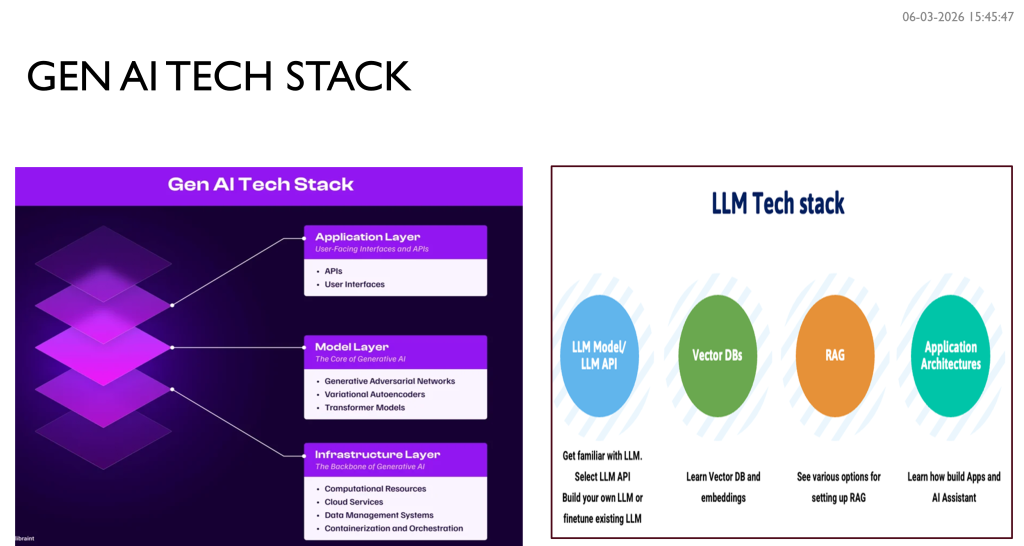
- The New Stack: Understanding vulnerabilities in the Generative AI architecture (Infrastructure vs. Model vs. App layer).
- The “Why” of Security: A panel discussion on why automated cycles still need human-in-the-loop governance.
- Deep Dive: Decoding the OWASP Top 10 for LLMs (Prompt Injection, Model Poisoning, etc.).
- Demo: A first look at Garuda, a cost-effective, NLP-driven code scanning tool for startups.
A Journey of Resilience and “Tech for Good”
Anupama Itikirala opened the session with a powerful personal narrative. With 30 years in the industry—including stints at Intel, Oracle, and GE—she shared her journey of restarting her career after a 2016 break.
Now a celebrated consultant and mentor, Anupama’s work is driven by “Tech for Good.” she emphasizes that technology must be inclusive, ethical, and, above all, secure.
The New Threat Landscape: Gen AI & the OWASP Top 10
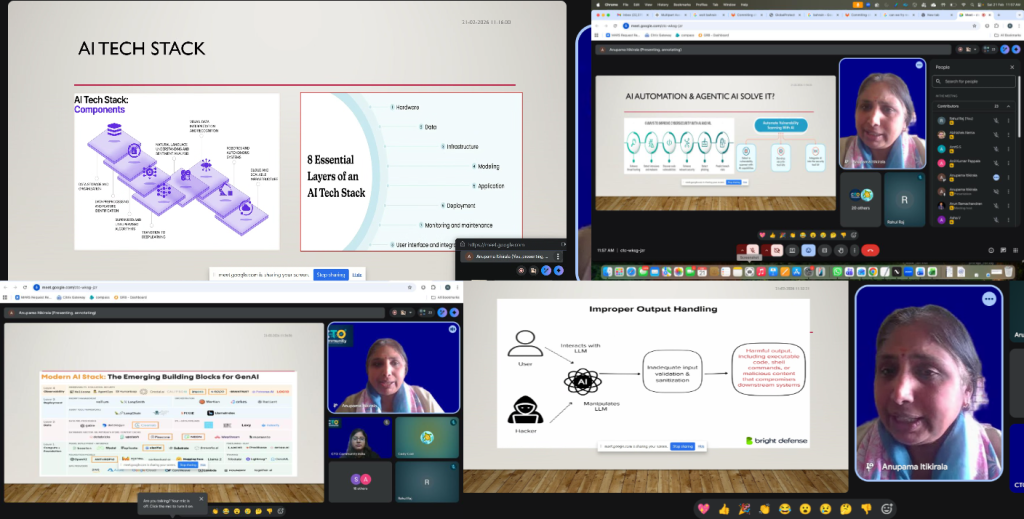
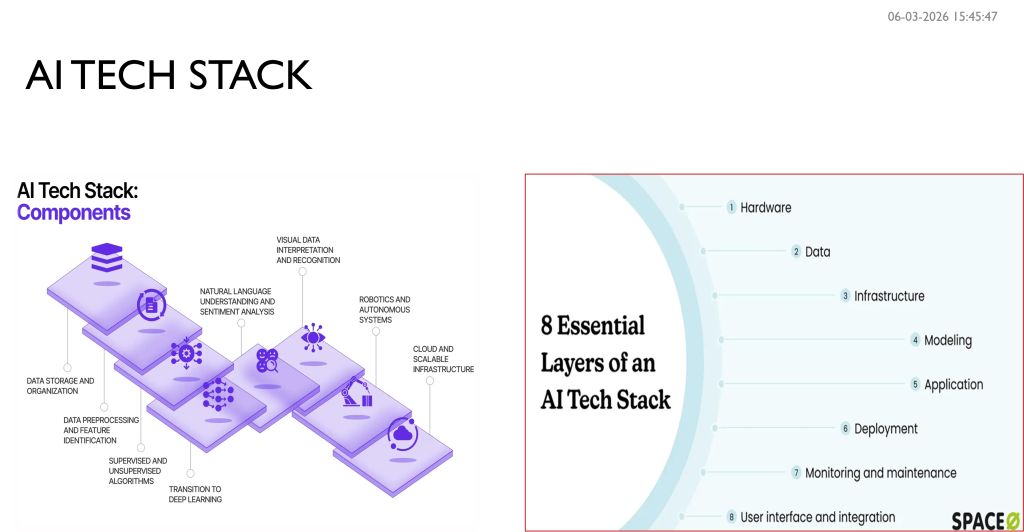
The transition from predictive analytics to Generative AI has drastically expanded the attack surface. Anupama, broke down the critical evolution of the tech stack.
Key Technical Takeaways:
- Vulnerability vs. Risk: Vulnerability is the weakness; Threat is the actor; Risk is the impact.
- The LLM Vulnerability Shift: Unlike traditional relational databases, Gen AI relies on unstructured data and complex “orchestration” layers, creating new backdoors.
- The OWASP Top 10 for LLMs: The session highlighted critical risks:
- Prompt Injection: Malicious inputs designed to override AI safety guards.
- Model Poisoning: Manipulating training data to create systemic biases or backdoors.
- Excessive Agency: Granting AI “agents” too much power without a “human-in-the-loop” to verify actions.
“Security is no longer a ‘nice-to-have’ in industries like automotive, a Bluetooth backdoor isn’t just a data leak; it’s a life-threatening risk.” — Abhishek Nema (CTO Community Member)
Innovation Spotlight: Project Garuda
In a standout segment, she demonstrated Garuda, her custom-built code scanning tool. Designed specifically for small companies and startups that find enterprise licensing (like SonarQube) prohibitive, Garuda offers:
- NLP-Driven Heuristics: Uses programming language parsers to build abstract syntax trees.
- Real-time Intelligence: Syncs with the National Vulnerability Database (NVD) twice daily.
- Cost-Effectiveness: A service-based model that prioritizes resource support over expensive tool licenses.
Looking Ahead: What’s Next for the Community?
As the session concluded, the room buzzed with ideas for future deep dives. The community is looking toward:
- Testing LLMs: Addressing the “Black Box” nature of model outputs.
- RAG Implementation: Refining Retrieval-Augmented Generation for better information reliability.
- Indic Languages: Solving the security gap for non-English NLP databases.
A Note of Gratitude
We extend a heartfelt Thank You to our guest speaker, Anupama Itikirala, for sharing her deep technical expertise and inspiring career journey. Her passion for mentorship and “tech for good” is a beacon for our CTO community.
We also thank our active participants, whose insights into business continuity and automotive safety added invaluable layers to the discussion. It is your engagement that makes these sessions a powerhouse of collective wisdom.
Call to Action: Secure Your Future
Don’t let your innovation be derailed by a late-night security alert.
Join the Next Deep Dive: We are currently planning sessions on LLM Testing and RAG Implementation. Stay tuned for the invite!
Adopt “Secure by Design”: Whether you are a solo founder or an enterprise lead, integrate security filters and “human-in-the-loop” checkpoints today.
We encourage all members to adopt “Secure by Design” principles—especially those in the startup phase where ROI often overshadows safety.